Routing Protocol

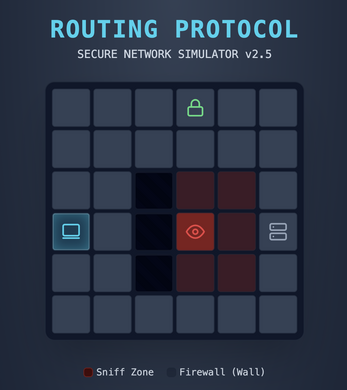
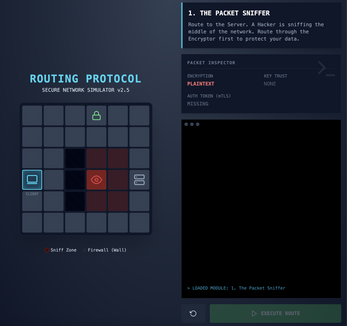
A cybersecurity puzzle game where you design network routes to deliver a data packet safely from client to server. You must avoid hacker sniffing zones, collect encryption keys, and obtain authentication tokens – all while obeying the rules of a zero‑trust network. The game simulates real‑world network security concepts in a minimalist, digi‑punk interface.
How to Play
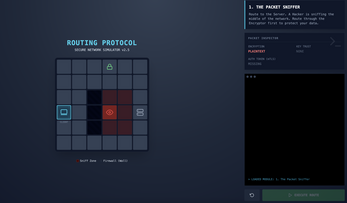
- Draw a path – Tap/click the client tile, then drag through adjacent tiles (up, down, left, right) to reach the server.
- Follow the rules – You cannot cross walls or step directly on hackers.
- Hackers have a 3×3 sniff zone; entering it without a good encryption key will expose your data and fail the mission.
- Collect green encryption keys (good) to protect your payload.
- Red keys (bad) will encrypt your data with a honeypot key – safe‑looking but the hacker can still break it.
- In later levels, you must also grab an auth token (mTLS), or the server will drop your packet.
- Execute – Once the path connects client-to-server, hit Execute Route and watch the packet travel step‑by‑step, checking each tile.
- Learn from failure – The terminal log explains exactly why a route failed, teaching you how to improve.
- Mental & Psychological Skills Improved Strategic Planning & Routing – You learn to think ahead, plan multi‑step paths, and anticipate risks.
- Logical Reasoning – Understanding the order of operations (encrypt before crossing a sniff zone, authenticate before reaching the server) strengthens logical sequencing.
- Problem‑Solving under Constraints – Walls, multiple hackers, and limited paths force you to find creative solutions – like backtracking or taking longer, safer routes.
- Cybersecurity Intuition – You internalise key security concepts (AES‑256, mTLS, honeypots, zero‑trust architecture) in a practical, visual way.
- Resilience & Trial‑Error Learning – Failing is part of the game; each attempt improves your understanding and builds a growth mindset.
- Attention to Detail – Spotting fake keys vs. real keys trains focused observation.
- Working Memory – You must hold the state of your packet (encrypted? authenticated?) in mind while building the path.
- The game transforms abstract network security into a tangible, addictive puzzle – making you a sharper thinker in both tech and everyday logic.
| Published | 2 days ago |
| Status | Released |
| Platforms | HTML5 |
| Author | JOE |
| Genre | Puzzle, Simulation |
| Tags | 2D, Brain Training, connection, connector, cybersecurity, in-browser, link, mobile |
| Links | GitHub |
| AI Disclosure | AI Assisted, Code, Graphics, Sounds, Text |

Leave a comment
Log in with itch.io to leave a comment.